ESET APT Activity Report Q2 2024–Q3 2024 summarizes notable activities of selected advanced persistent threat (APT) groups that were documented by ESET researchers from April 2024 until the end of September 2024. The highlighted operations are representative of the broader landscape of threats we investigated during this period, illustrating the key trends and developments, and contain only a fraction of the cybersecurity intelligence data provided to customers of ESET’s private APT reports.
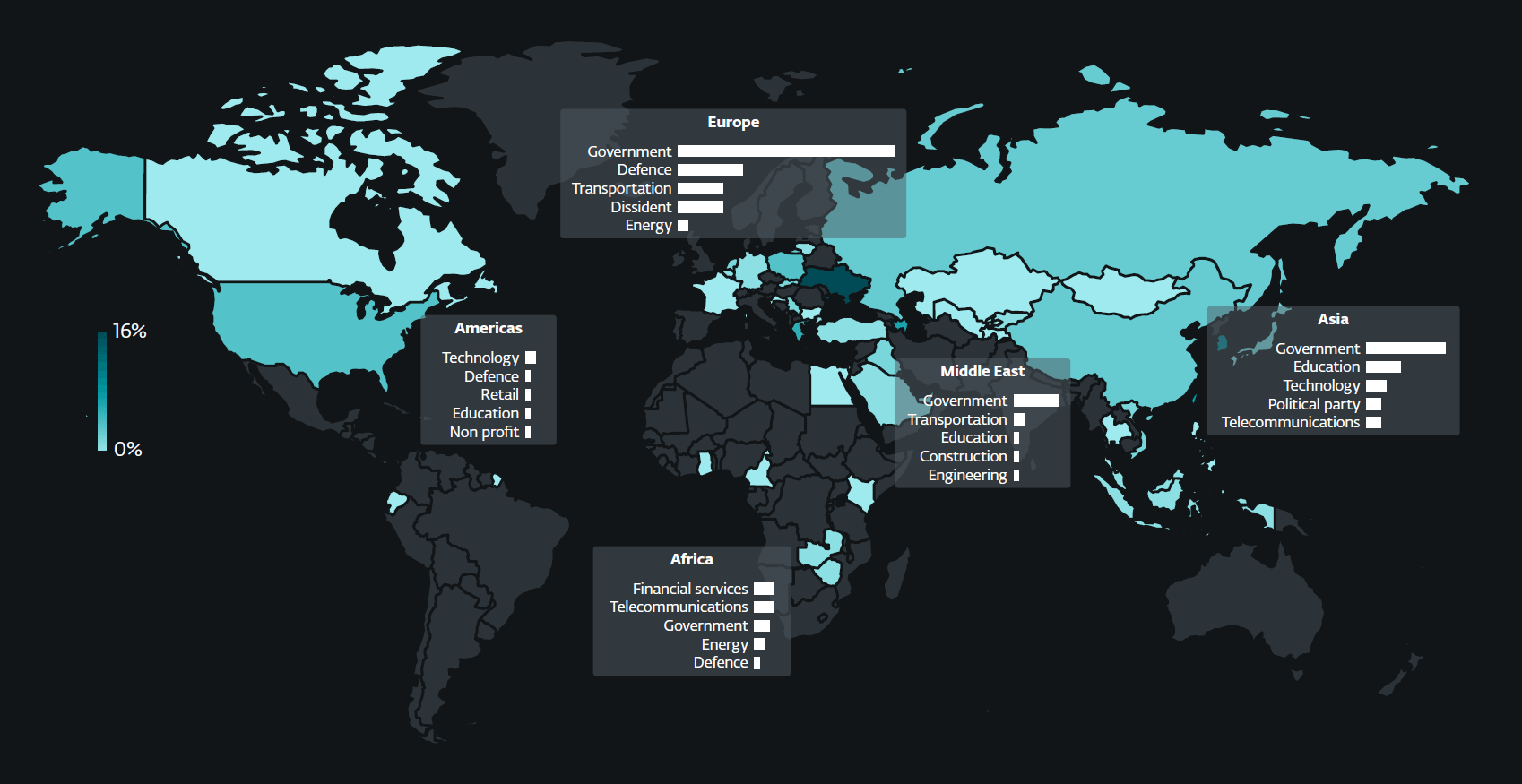
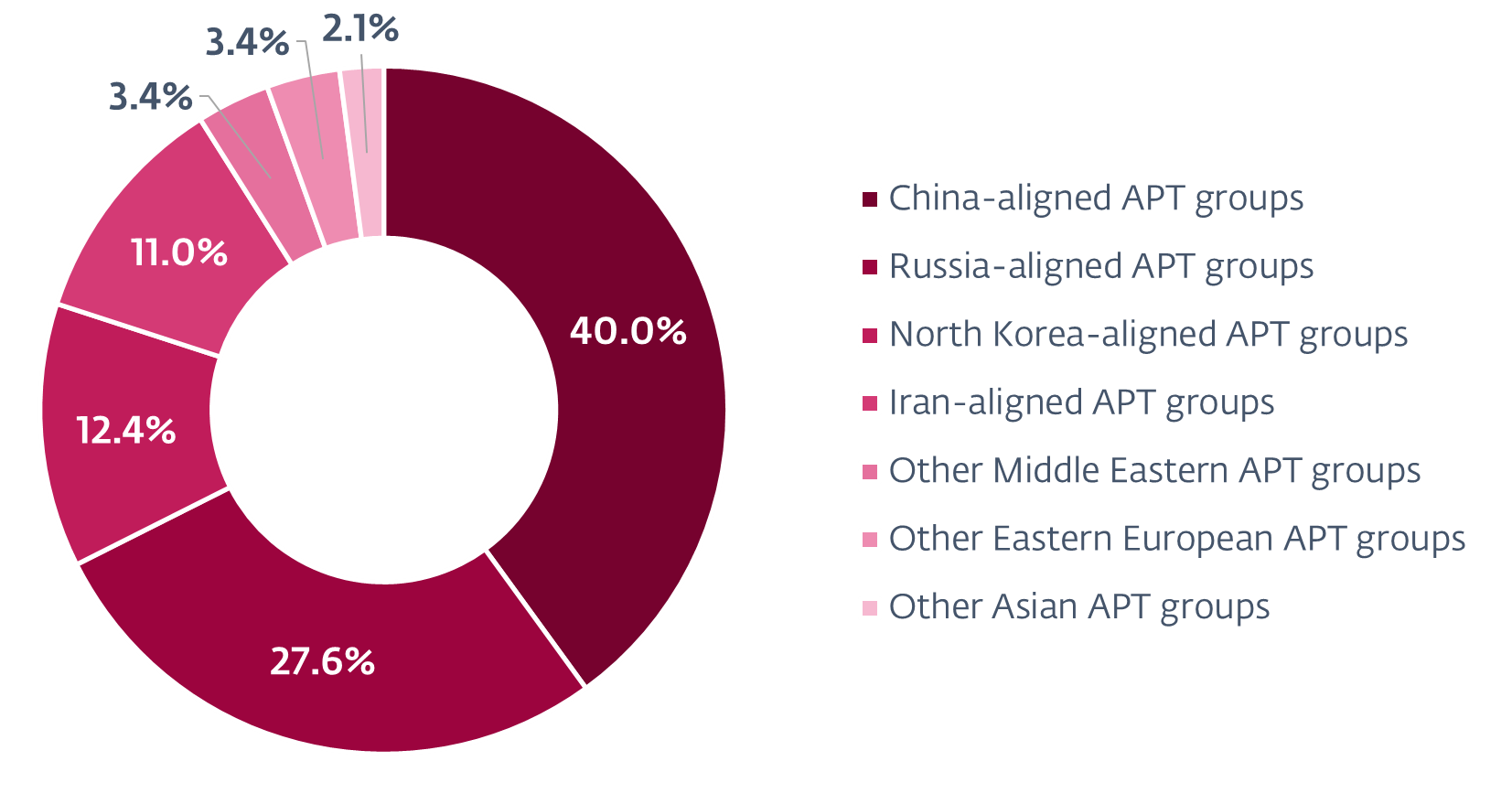
During the monitored period, we observed a notable expansion in targeting by China-aligned MirrorFace. Typically focused on Japanese entities, it extended its operations to include a diplomatic organization in the European Union (EU) for the first time while continuing to prioritize its Japanese targets. Additionally, China-aligned APT groups have been relying increasingly on the open-source and multiplatform SoftEther VPN to maintain access to victims’ networks. We detected extensive use of SoftEther VPN by Flax Typhoon, observed Webworm switching from its full-featured backdoor to using the SoftEther VPN Bridge on machines of governmental organizations in the EU, and noticed GALLIUM deploying SoftEther VPN servers at telecommunications operators in Africa.
We also observed indications that Iran-aligned groups might be leveraging their cybercapabilities to support diplomatic espionage and, potentially, kinetic operations. These groups compromised several financial services firms in Africa – a continent geopolitically important to Iran; conducted cyberespionage against Iraq and Azerbaijan, neighboring countries with which Iran has complex relationships; and increased their interest in the transportation sector in Israel. Despite this seemingly narrow geographical targeting, Iran-aligned groups maintained a global focus, also pursuing diplomatic envoys in France and educational organizations in the United States.
North Korea-aligned threat actors persisted in advancing the goals of their regime, which has been accused by the United Nations and South Korea of stealing funds – both traditional currencies and cryptocurrencies – to support its weapons of mass destruction programs. These groups continued their attacks on defense and aerospace companies in Europe and the US, as well as targeting cryptocurrency developers, think tanks, and NGOs. One such group, Kimsuky, began abusing Microsoft Management Console files, which are typically used by system administrators but can execute any Windows command. Additionally, several North Korea-aligned groups frequently misused popular cloud-based services, including Google Drive, Microsoft OneDrive, Dropbox, Yandex Disk, pCloud, GitHub, and Bitbucket. For the first time, we saw an APT group – specifically ScarCruft – abusing Zoho cloud services.
We detected Russia-aligned cyberespionage groups frequently targeting webmail servers such as Roundcube and Zimbra, usually with spearphishing emails that trigger known XSS vulnerabilities. Besides Sednit targeting governmental, academic, and defense-related entities worldwide, we identified another Russia-aligned group, which we named GreenCube, stealing email messages via XSS vulnerabilities in Roundcube. Other Russia-aligned groups continued to focus on Ukraine, with Gamaredon deploying large spearphishing campaigns while reworking its tools using and abusing the Telegram and Signal messaging apps. Sandworm utilized its new Windows backdoor, which we named WrongSens, and its advanced Linux malware: LOADGRIP and BIASBOAT. Additionally, we detected Operation Texonto, a disinformation and psychological operation primarily aimed at demoralizing Ukrainians, also targeting Russian dissidents. We also analyzed the public hack-and-leak of the Polish Anti-Doping Agency, which we believe was compromised by an initial access broker who then shared access with the Belarus-aligned FrostyNeighbor APT group, the entity behind cyber-enabled disinformation campaigns critical of the North Atlantic Alliance. Finally, from analyzing an exploit found in the wild, we discovered a remote code execution vulnerability in WPS Office for Windows. We attribute the attack leveraging the exploit to the South Korea-aligned APT-C-60 group.
Malicious activities described in ESET APT Activity Report Q2 2024–Q3 2024 are detected by ESET products; shared intelligence is based mostly on proprietary ESET telemetry data and has been verified by ESET researchers.
ESET APT Activity Reports contain only a fraction of the cybersecurity intelligence data provided in ESET APT Reports PREMIUM. For more information, visit the ESET Threat Intelligence website.
Follow ESET research on Twitter for regular updates on key trends and top threats.