“Everybody has a plan until they get punched in the mouth.”
Mike Tyson’s punchy (pun intended) adage rings all too true for organizations reeling from a ransomware attack. In recent years, ransomware has proven capable of bringing even a thriving business to its knees in a matter of hours, and it’s safe to say that it will continue to sucker-punch organizations of all stripes, testing their cyber-mettle and contingency plans in ways few other threats can match.
There’s no shortage of data and actual incidents to bear this out. According to Verizon’s 2024 Data Breach Investigations Report, one-third of all data breaches involve ransomware or another extortion technique. "Ransomware was a top threat across 92% of industries," reads the report.
If this sounds disconcerting, it’s because it is. The stakes are also high because ransomware may also come on the back of a supply chain attack – as was the case with the Kaseya incident in 2021 that exploited a vulnerability in the company’s IT management platform to vastly amplify the reach of ransomware across an untold number of organizations worldwide.
Bruised and battered
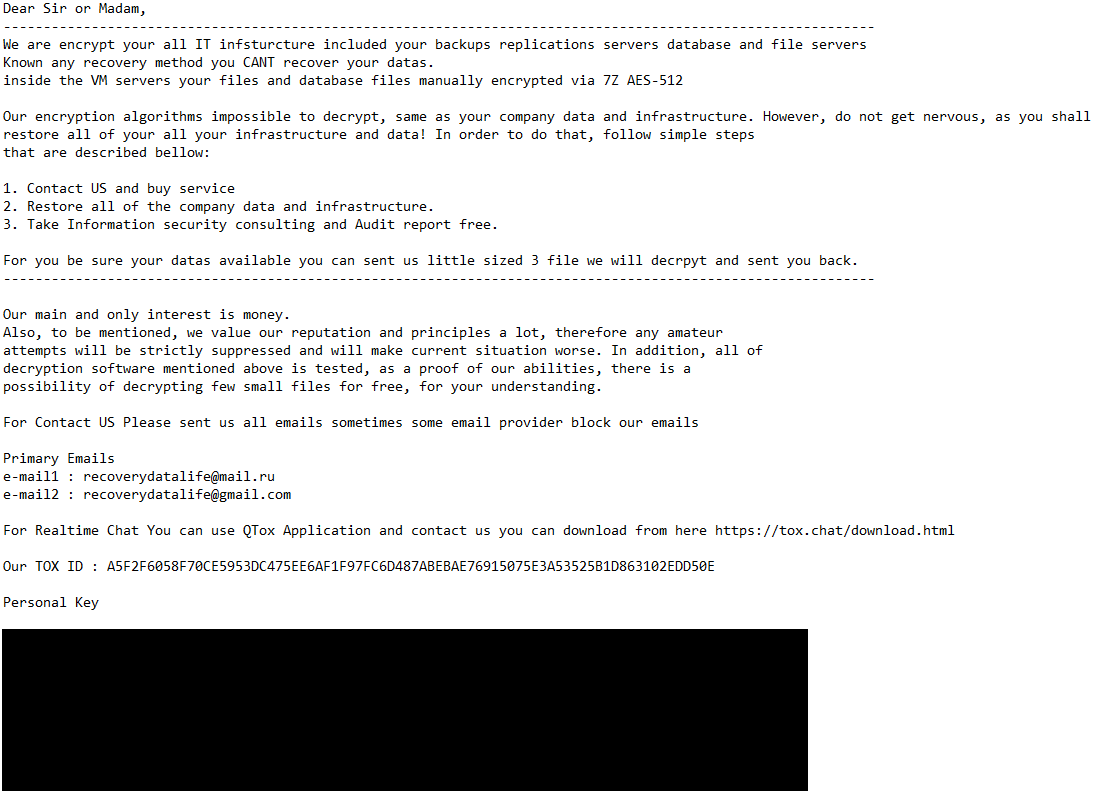
When the news of a ransomware attack breaks, headlines often focus on the dramatic ransom demands and the ethical and legal conundrums over payment. What they often fail to capture, however, is the organizational and human trauma suffered by the victims, doubly so when the incident is compounded by data exfiltration and threats to make the stolen data public.
When systems go dark, businesses don’t simply pause – they hemorrhage money while watching new opportunities slip away and brand reputation suffer. The wounds deepen exponentially as frantic recovery efforts stretch from hours into days, weeks and possibly even months. The brutally simple premise of ransomware – encrypt critical business data and demand payment for its release – actually belies a complex cascade of operational, financial and reputational damage that unfolds in the wake of the attack.
Again, there is ample data to show that a successful ransomware incident costs victims dearly. IBM’s Cost of a Data Breach Report 2024, for example, puts the average cost of recovery from such an attack at close to US$5 million.
Throwing a lifeline
Organizations hit by ransomware typically rely on three escape routes: restoring from backups, receiving a decryption tool from security researchers (such as those involved with the No More Ransom initiative, which includes ESET as a member) or paying the ransom in return for a decryptor. But what if none of these options turns out to be workable?
First, attackers often tighten the screw on victims by targeting also their backup systems, corrupting or encrypting them before deploying ransomware on production environments. Second, decryption tools from researchers are better thought of as a last-resort option as it often cannot match the urgency of business recovery needs.
What about throwing in the towel and paying the ransom? Leaving aside the possible legal and regulatory pitfalls, payment guarantees exactly nothing while often just adding insult to injury. Colonial Pipeline learned this the hard way when the decryption tools provided to it in exchange for a ransom payment of US$4.4 million were so shoddy that restoring systems from backups turned out to be the only viable option anyway. (Note: the U.S. Department of Justice later recovered most of the ransom.)
ESET Ransomware Remediation brings a new approach to this conundrum, effectively combining prevention and remediation into one. It creates targeted file backups that are out of reach for bad actors during a process that kicks in when the risk is straight ahead; i.e., once a possible ransomware attempt is detected. Since attackers also often take aim at data backups, this approach addresses the risk of unknowingly relying on compromised backups.
Bracing for impact
Ransomware is a full-blown disruptor capable of unraveling business operations thread by thread and with alarming speed. That said, organizations with tried-and-true prevention and recovery capabilities will not only survive in the face of ransomware attacks and other threats – their ability to sidestep such blows may become their ultimate competitive advantage.
In the ever-shifting digital landscape, change is the only constant, and resilience hinges on anticipating the unexpected. Plan for the unknown like your business depends on it – because it does.