A team of academics from the University of California, Irvine (UCI), have presented a type of attack that could enable a malefactor to retrieve sensitive information you entered via your keyboard – possibly up to a minute after you typed it.
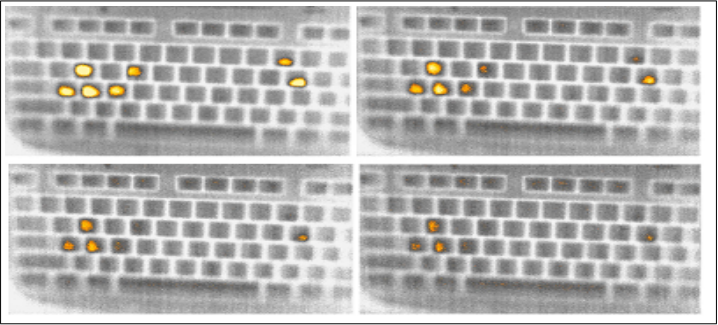
The researchers had 30 users enter 10 different passwords, both strong and weak, on four common external keyboards. Using a thermal imaging camera, the researchers then scanned the residual heat left on the recently-pressed keys. In the second stage, they enlisted the help of eight non-experts in the field who, acting as “adversaries”, were asked to derive the set of pressed keys from the thermal imaging data – which they reliably did.
Long story short, the subjects successfully retrieved entire sets of key-presses that were captured by the camera as late as 30 seconds after the first key was entered. In addition, recovery of a partial set of key-presses was possible one minute after the first key was pressed, according to the researchers, who described their findings in a paper called “Thermanator: Thermal Residue-Based Post Factum Attacks On Keyboard Password Entry”. The pieces of the puzzle thus obtained could be easily leveraged for password-cracking attacks.
Password "passw0rd" thermal residue on the keyboard after 0, 15, 30, and 45 seconds after entry (University of California, Irvine)
"If you type your password and walk or step away, someone can learn a lot about it after-the-fact," said one of the paper’s authors, Gene Tsudik.
"Being warm-blooded, human beings naturally prefer environments that are colder than their internal temperature," reads the paper. "Because of this heat disparity, it is inevitable that we leave thermal residue on numerous objects that we routinely touch, especially, with bare fingers."
A study back in 2011 showed that PIN codes entered on cash machines can also be recovered by analyzing the residual heat left behind on the keypads.
Meanwhile, the study on "Thermanator" also revealed that hunt-and-peck typists would be particularly susceptible to this attack, given the larger fingerprint and thermal trace that they leave on each key. Touch typists are safer, since they create more thermal noise by resting their fingers on the “home row” (i.e. "ASDF" and "JKL;" keys for the left and right hands, respectively).
A number of conditions need to be met for the attack to work. Notably, the victim must step away or be enticed away from their system shortly after inputting their sensitive information, and the camera must have an uninhibited view of the keyboard.
Either way, according to the paper, this “new post factum insider attack” poses a new credible threat for password-based systems, not least because “formerly niche sensing devices become less and less expensive”.
Mitigations
The paper suggests a number of mitigations that should make retrieving the data impossible or at least much more difficult. They include running one’s hands along the keyboard after inputting sensitive information or typing random “chaff” in order to introduce “thermal noise” into the residues left on key presses.
Other “antidotes” include using the mouse to select password characters on an on-screen keyboard. However, this may in turn increase your exposure to shoulder-surfing attacks, where someone peeks over your shoulder while you input sensitive information.
Additional – but apparently rather impractical countermeasures – include wearing insulating gloves. Or even fake nails, as the study found that wearing long acrylic fingernails was enough to be immune to Thermanator. We wouldn’t blame you if you opted for a different countermeasure, however.